As soon as the world witnessed technological advancements, each sector where humans once struggled has been transformed into an easier and efficient system. The majority of these transformations were noticed in the business sector. The most significant advantage a business has out of these innovations would be its absolute data safety, as it is most important to keep secure for the competitors.
Even before these inventions were made, people struggled a lot to keep their data safe. These measures grow grave for B2Bs, as their constant communication is with other businesses, and data protection was essential to build in the solutions offered because a single breach would cause a big strain to the reputation, brand loyalty, and marketing in the society.
Thus it is an essential step for SMEs to define and improve their cybersecurity stages and invest in such security measures to get ensured benefits. Here I’ve included various and satisfactory benefits of investing in modern network security approaches.
What are Cyber Security Measures for B2Bs?
Cybersecurity approaches for any business comprise the modern tools and technologies, process and operations, along with software and mobile applications to come together to prevent any outer body, individual, or system from breaching its information. These systems tend to provide the data security that a business cannot ensure manually to employees’ data, network, and ongoing processes.
What is the Need for Cyber Security Measures for Businesses?
I would like to make it clear why it is so essential for B2Bs to ensure data safety because no one is actually safe from this cybersecurity. That said, according to reports of 2018, around 67% of small enterprises faced internet attacks while 58% experienced data violations.
These breaches and attacks actually reflect the vulnerability of the processes and businesses, which creates doubt and obstacles in the process of partnerships. Not only the customers but the workers and business partners do not appreciate it. And thus, to be in the race of top-quality products and services offered by B2B companies, it is essential in this modern world to offer alongside guaranteed security.
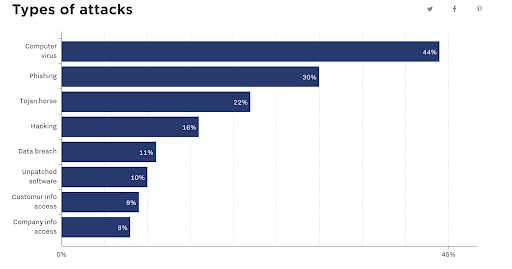
The image shows the different types of attacks and their ratios that happen inside any business.
After learning the importance of network security, let’s move ahead towards the benefits of these arrangements for B2Bs.
Benefits of Cyber Security Measures
Well, apart from just network safety, these measures tend to offer a lot of other benefits to businesses to business enterprises within their software solutions and services, which I have mentioned below. So let’s start with it.
Prohibits Identity Theft
One of the primary threats to any person or business is for their identity as one knows the importance of personal identity, which can let one crack the most extensive passwords, vaults, accounts, and many other areas and essential access information buried deep. For example, these could be even the nuclear codes of any nation. But considering business, identity theft for various accounts, employee information, etc., is just as important as the nuclear codes.
Corruption of all the information mentioned above poses a high failure and can also cause a lot of harm to the B2B identity. This corrupt data can be due to manual mistakes, software hacking or malware, or hardware dysfunctioning. As a major solution to these, it becomes essential to plan and create data backup and recovery so that you still have a grip over all your information.
But as a security option to this, B2B companies help other businesses in configuring approaches along with their solutions to set cloud backup and recovery actions and prevent identity theft or data corruption. Following are the benefits offered in preventing identity crises in your business.
- More and more businesses can choose your security options and help you close more deals as a sign of trust and security.
- Investing in such measures can help businesses save time, money, and manual efforts due to the backup and recovery actions.
- Builds a more professional identity for such high measures.
Restricts Unauthorized Access and Data Manipulation
With the increase in usage of software applications and programs in daily routine, the data vulnerability is also increased as one can easily break into the system with malware and hacking. B2Bs hence need a solution that is secured, restricts unauthorized access of any person even inside the organization, and data violation.
One of the prominent tasks of businesses occurring repetitively is crediting their employees’ salary and maintaining other personal information. But considering these advancements, the FactoHR’s payroll software by these businesses can ensure their data safety from falling into outsider’s hands. Thus more focus is given to the application and software security features by the B2Bs for their operations.
Here are the ways an application embedded with cyber safety measurements can offer to businesses:
- Separate access IDs for different users to ensure unauthorized access and data manipulation in any form like stealing, deleting, or changing.
- In-built security options for keeping the data safe.
- Use of digital signatures and approvals for enhanced data safety and authenticity.
- Cryptographic tools to ensure risk management and avoid alterations and modifications without superior permissions.
Protects Employee and Business Sensitive Data
As mentioned in the above benefit, securing employees’ and businesses’ data is a top priority when investing in online solutions. And data breach can cause huge damage to the company, including corrupted mails, data leaks, etc. According to statistics for the previous ten years, a total of 300 data breaches with theft of 100,000 are recorded. Imagine your company’s meeting records, employees’ salary, client deals, etc. falling into the hands of your rivals.
The modern systems have evolved in such a way that data protection has become their primary goal to offer to B2Bs. With enhanced security and cloud storage options, businesses can hold onto their data within the system very securely, along with in-built recovery options.
Enhanced Security Defence Systems
Businesses can employ cybersecurity specialists for their defense systems, including internet networks, data centers, and system processes. These experts ensure the following:
- Enhances protection layers for outsiders to prevent them from penetrating boundaries.
- Constantly monitors the data risks and susceptibility and controls various attacks and illegal accesses.
- Sets up security protocols and updates data reliability systems.
- Manages the access for only authorized users.
- Troubleshoots and verifies the information changes and maintains active reports.
- Provide regular updates to the administrations and IT experts in the organization.
Improved Business Functions with increased ROI
As a result of all the above procedures, businesses can trust your security solutions and invest in them, which likely improves your customer support and returns on investments. Well, for expecting higher ROI, Employee information management solutions, Customer relation management, etc., can be made secured using these cybersecurity metrics.
Ending Notes
As with the modernizations on rising, new and exciting technologies are born that would help businesses to perform their operations with more efficiency. But along with this technology, the power of data breach and security thefts also evolved, making it complicated for business. But with the security measures, those businesses who deal with other businesses can offer ultimate security that would be challenging to breach.
Author Bio:
 Sweta is an experienced content strategist at FactoHR, having a keen interest in communication and the latest trends that are useful to entrepreneurs. Her passion for learning aids the team members in representing new ideas that later help businesses achieve their mission and vision.
Sweta is an experienced content strategist at FactoHR, having a keen interest in communication and the latest trends that are useful to entrepreneurs. Her passion for learning aids the team members in representing new ideas that later help businesses achieve their mission and vision.